DAO Security: A 2026 Guide to Preventing Governance Exploits

What is a DAO? (And Why is its Security Unique?)
Before we dive into the framework for securing your organization, let's get on the same page. A Decentralized Autonomous Organization, or DAO, is like a company that runs itself. Instead of a CEO and a board of directors, a DAO is governed by its members, and its rules are encoded directly into smart contracts on a blockchain. Think of it as a digital cooperative where token holders vote on every important decision, from treasury spending to protocol upgrades.

This structure is incredibly powerful, but it also creates a new class of risks. In a traditional company, a bad decision can be reversed by leadership. In a DAO, the smart contract code is the ultimate authority. This is often celebrated with the phrase "code is law," but it has a dangerous flip side: if there is a bug or a loophole in that code, that becomes the law, too. This is the core challenge of DAO security.
The Double-Edged Sword of Decentralization
This brings us to the unique nature of protecting a DAO. The very qualities that make a DAO great—its transparency and resistance to censorship—also create its biggest vulnerabilities. There is no central "off switch" or a support team you can call if an attack is in progress. An attacker can exploit a governance flaw to drain the treasury, and once the transaction is confirmed on the blockchain, it's often irreversible. You gain community control but must also prepare for complex new attack surfaces that traditional organizations never face.
The DAO Governance Attack Surface: Common Exploits in 2026
Understanding the structure of your DAO is the first step; now you need to know your enemy. The primary DAO security threats in 2026 involve exploiting governance rules and smart contract code. To build effective defenses, you first need to recognize the most common ways attackers can strike. Think of this as your threat intelligence briefing.
Flash Loan Governance Attacks
Imagine an attacker borrowing millions of dollars in your DAO's governance tokens with zero collateral, but only for a few seconds. That's a flash loan. In a single, atomic transaction, they can borrow the tokens, vote to pass a malicious proposal (like draining the treasury to their own wallet), and then repay the loan. If the proposal execution is tied to the vote, the damage is done instantly. Because it all happens in one transaction, they only need to pay a small fee to wield enormous, temporary voting power. This form of attack is a direct assault on the principle of one-token, one-vote.
Malicious Proposal Injection
Not all attacks are purely technical. Some are based on deception. An attacker might submit a proposal with a benign-sounding title like "Quarterly Protocol Maintenance Update" or "Fee Structure Optimization." However, the code attached to the proposal could contain a hidden function to transfer treasury funds or change critical protocol ownership to the attacker. If your community members vote 'yes' based on the title alone without carefully verifying the code, they can unknowingly approve a heist. Strong dao security depends on a vigilant and informed community.
Smart Contract Vulnerabilities
The code that runs your DAO is its foundation, and any cracks can bring the whole structure down. Vulnerabilities in the smart contracts themselves can bypass governance entirely. For example, a reentrancy bug might allow an attacker to vote multiple times with the same batch of tokens before the system can register their first vote. Simple logic errors, like a miscalculation in quorum requirements or vote tallying, can also be exploited to push through proposals that should have failed. These bugs undermine the integrity of the entire voting process.
Vote Buying and Sybil Attacks
This is a more brute-force approach to manipulating governance. A well-funded attacker can simply purchase a large number of governance tokens on the open market to gain significant voting power and force through self-serving proposals. A related threat is the Sybil attack, where one entity creates thousands of wallets with small amounts of tokens. While each wallet has little power, together they can be used to meet quorum on an otherwise unpopular proposal or create the illusion of widespread community support for a contentious idea.
Step 1: Fortifying Your Smart Contracts
Now that we've seen how governance attacks can unfold, let's begin building your defense. The absolute bedrock of your DAO's security is its code. A clever governance system is worthless if it's built on a foundation of flawed smart contracts. This first step is all about making that foundation as solid as possible before you even consider deploying.
Conduct Professional Audits (and Make Reports Public)
Before your code ever touches the mainnet, you need to have it professionally audited. Think of this as getting a second, third, and even fourth pair of expert eyes on your work. Don't stop at just one audit; different firms have unique specializations and may catch things others miss. After the audit, publish the full report for your community to see. This transparency builds trust and shows you are serious about common smart contract vulnerabilities and overall DAO security.
Use Battle-Tested Frameworks
The temptation for developers to write everything from scratch is strong, but it introduces unnecessary risk. Instead of reinventing core governance logic, build upon well-vetted, open-source frameworks. Libraries like OpenZeppelin's Governor contracts have been used in countless projects and scrutinized by thousands of developers. By using them, you inherit their security properties and avoid introducing simple but costly bugs.
Implement a Bug Bounty Program
Your security work isn't finished at deployment. A bug bounty program provides a powerful, ongoing incentive for ethical hackers to find and report vulnerabilities before malicious actors can exploit them. By offering a financial reward for responsibly disclosed bugs, you turn a global community of security researchers into your allies. This creates a continuous, crowdsourced audit of your live code, making your entire system more resilient over time.
Step 2: Implementing Strong Access Controls & Timelocks
With your smart contract foundation secured, your next move is to build in checks and balances. Think of these controls as critical circuit breakers for your governance system. They provide a vital layer of dao security by creating intentional delays and requiring collective action, giving your community time to react to threats.
The Power of Timelocks
A timelock is a simple yet powerful smart contract that enforces a mandatory delay between when a governance proposal passes and when its code can actually be executed. This waiting period is your community's safety net. It creates a critical window for members to spot a malicious or flawed proposal that slipped through the vote, organize a response, and prevent a potential disaster before it happens.
Multi-Sig Wallets for Treasury Management
For your treasury, a multi-signature (multi-sig) wallet is non-negotiable. Instead of a single person holding the keys to the funds, a multi-sig requires a minimum number of trusted signers to approve any transaction. For example, you might set up a 3-of-5 wallet, where any three of the five designated keyholders must agree to move funds. This decentralizes control and dramatically reduces the risk of a single point of failure from a hack or a rogue actor.
Step 3: Designing a Resilient Governance Framework
With your smart contracts audited and access controls in place, it’s time to architect the rules of your DAO. A well-designed governance system is your primary defense against manipulation and hostile takeovers. Think of these parameters as the constitution of your organization; they define how decisions are made and can prevent bad actors from hijacking the process before it even begins. Getting these settings right is fundamental to your long-term DAO security.
Set Sensible Quorum and Proposal Thresholds
Your first line of defense is setting smart participation requirements. A proposal threshold is the minimum number of tokens a member must hold to submit a proposal. This stops spam and low-effort proposals. A quorum is the minimum percentage of the total voting supply that must participate for a vote to be valid. You need to find a sweet spot. Set these too low, and a small group could easily pass a malicious proposal. Set them too high, and you risk voter apathy leading to gridlock where no decisions can be made.
Consider Voting Delays and Periods
Timing is everything. A voting delay, also known as a review period, is a mandatory waiting period between when a proposal is submitted and when voting begins. This simple delay is a powerful tool against flash loan attacks, where an attacker borrows a huge number of tokens, votes, and returns the loan in a single transaction. By requiring tokens to be held for the duration of the delay and the voting period, you force attackers to have real, sustained capital at risk, making such attacks economically unfeasible.
Explore Novel Voting Mechanisms
The standard "one token, one vote" system can sometimes concentrate power with a few large holders. As your DAO matures, you might want to explore alternative systems. Mechanisms like quadratic voting give more weight to the number of participants rather than the number of tokens they hold, promoting broader consensus. Conviction voting allows members to signal their preferences over time, giving more weight to long-term, sustained support. While more complex to implement, these systems can create a more equitable and secure decision-making environment.
Step 4: Continuous Monitoring & Incident Response Planning
Your work isn't done after launching. Strong dao security is a living process, not a one-time setup. Once your governance framework is active, you need to keep a vigilant eye on it and have a clear plan for when things go wrong—because in Web3, it's a matter of "when," not "if."
Use On-Chain Monitoring Tools
You can’t watch the blockchain 24/7, but automated tools can. Services like OpenZeppelin Defender and Forta continuously scan for suspicious on-chain activity related to your DAO. They can send you real-time alerts for unusual proposal submissions, large token movements, or contract interactions, giving you a critical head start to react to a potential threat.
Create a Clear Incident Response Plan
When an exploit is underway, panic is your enemy. You must prepare a public incident response plan before you need it. This document should clearly outline who the community should contact, the immediate steps the core team will take, and how decisions will be made under pressure. A key part of this is having a clear dispute resolution process to handle the aftermath.
The Future of DAO Security: AI Audits and Formal Verification
Building a secure DAO is an ongoing process, not a one-time setup. As you continue to monitor and adapt your governance framework, it's smart to keep an eye on the exciting advancements shaping the future of DAO security. New technologies are emerging to automate and strengthen your defenses against increasingly sophisticated attacks.
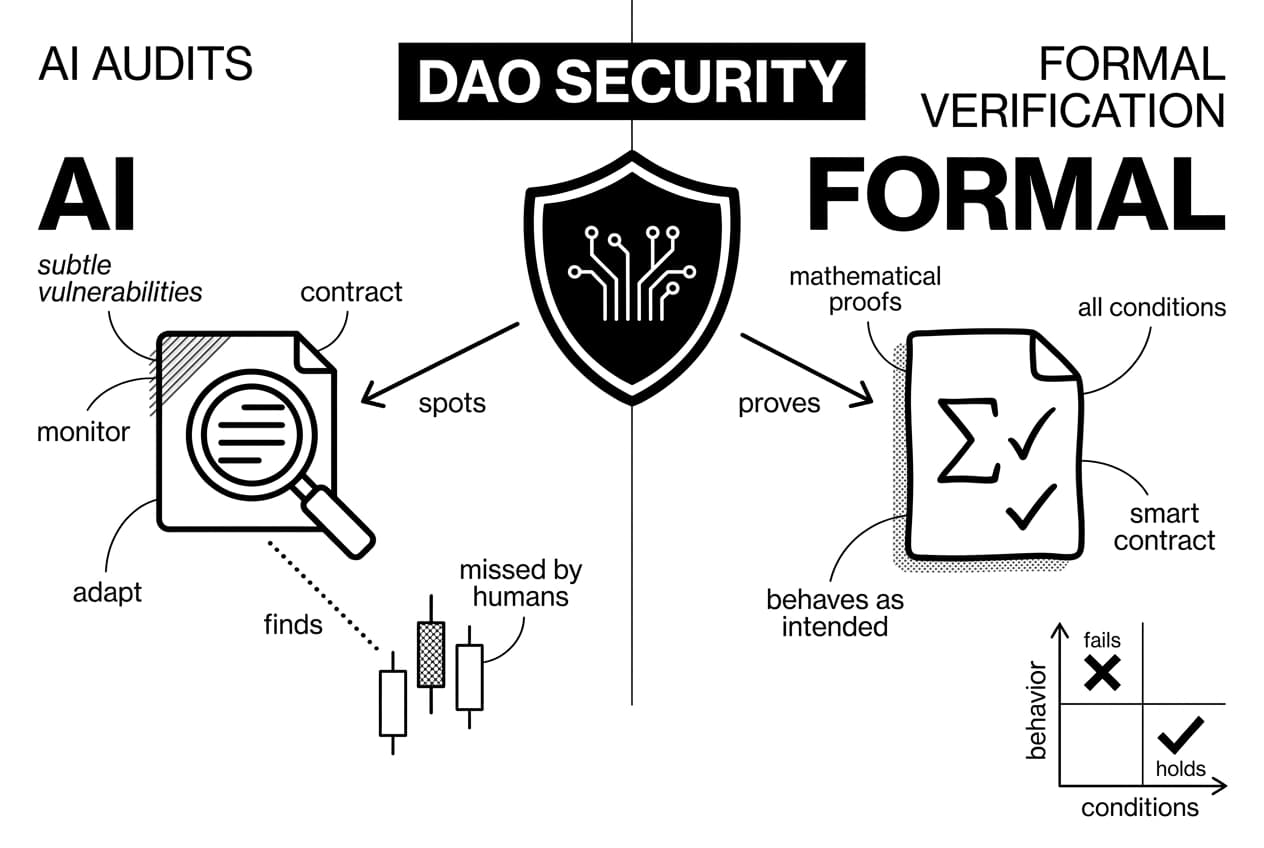
For instance, AI-powered auditing tools are becoming more effective at spotting subtle vulnerabilities that human auditors might miss. Another promising area is formal verification, which uses mathematical proofs to confirm that a smart contract behaves exactly as intended under all conditions. Staying informed about these developments will help you keep your organization ahead of tomorrow's threats.
Frequently Asked Questions
- What is a DAO in cyber security?
- In cybersecurity, a DAO is an organization run by transparent smart contracts. This transparency makes it a unique target, as attackers can analyze its code for vulnerabilities. Its decentralized nature means there is no central admin to quickly patch flaws, making robust, pre-launch security audits and design absolutely critical.
- What does DAO stand for?
- DAO stands for Decentralized Autonomous Organization. "Decentralized" means it operates without a central leader or entity. "Autonomous" means it runs on its own based on pre-written smart contracts. "Organization" refers to the community of members working together toward a shared goal according to these automated rules.
- Is a DAO a security?
- Whether a DAO's token is a security is a complex legal question that depends on the jurisdiction. In the U.S., regulators like the SEC may apply the Howey Test to see if it's an investment contract. The legal landscape is still evolving, so it's best to consult a legal expert.
- What are the top 5 DAOs?
- The "top" DAOs change, but well-known examples include Uniswap, which governs a leading decentralized exchange, and MakerDAO, which manages the DAI stablecoin. Others like Aave (lending) and Lido (liquid staking) are also highly influential. Rankings often depend on factors like treasury size, member activity, and protocol influence.
Sources
Author

Crypto analyst and blockchain educator with over 8 years of experience in the digital asset space. Former fintech consultant at a major Wall Street firm turned full-time crypto journalist. Specializes in DeFi, tokenomics, and blockchain technology. His writing breaks down complex cryptocurrency concepts into actionable insights for both beginners and seasoned investors.