Wallet Drainer Guide (2026): How Scammers Steal Your Crypto

What is a Wallet Drainer?
A wallet drainer is malicious code, often hidden inside a seemingly legitimate website or decentralized application (dApp), that tricks you into approving transactions which empty your cryptocurrency wallet. It is a sophisticated digital trap designed to steal your assets in a single, devastating moment. The rise of these scams has become one of the most significant security threats in the Web3 space, costing users millions of dollars each year.
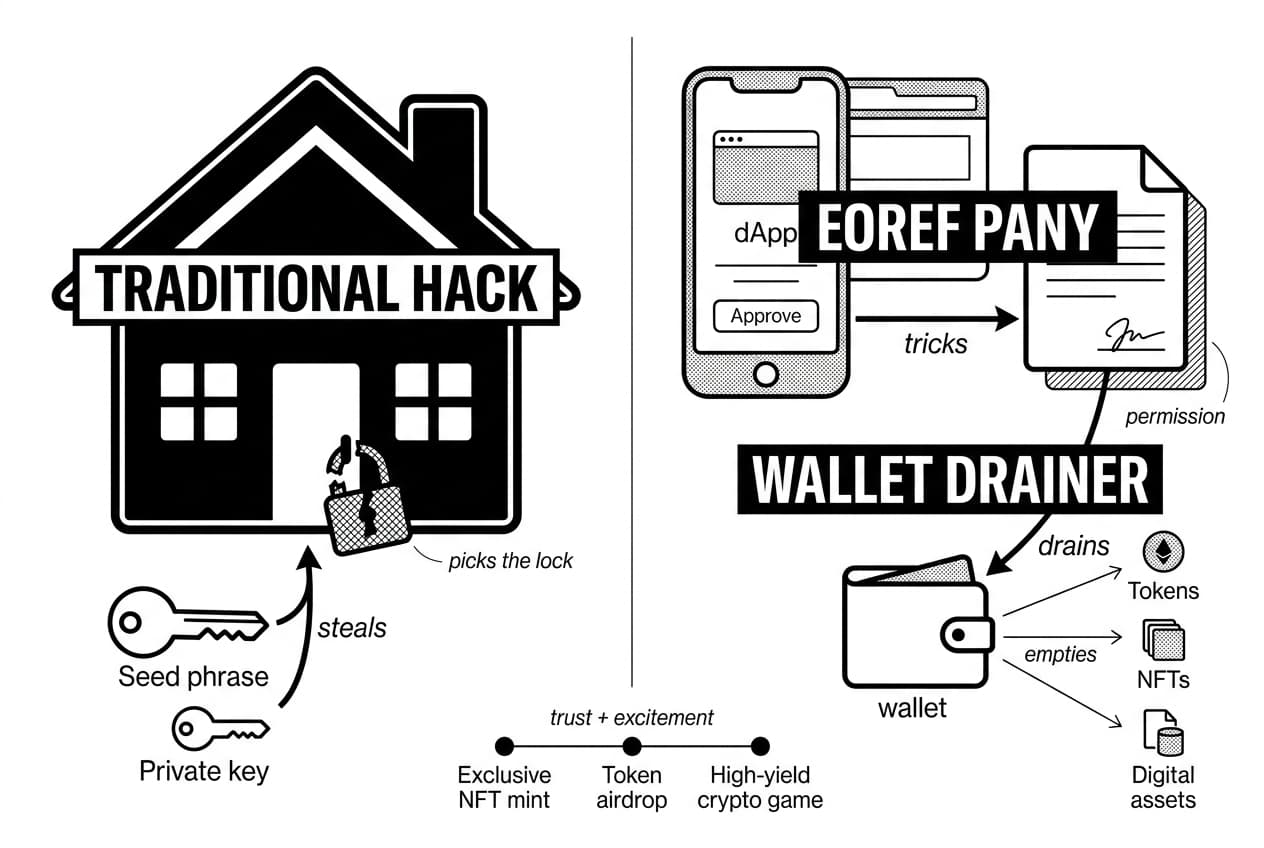
Why does this matter so much? Because a wallet drainer crypto attack doesn't just steal a small amount; it aims to take everything. Imagine logging on to check your portfolio, only to find all your tokens, NFTs, and digital assets gone without a trace. This is the reality for victims. The attack preys on trust and excitement, often appearing as an exclusive NFT mint, a new token airdrop, or a high-yield crypto game. By understanding how wallet drainers work, you can build the first line of defense to protect your hard-earned digital wealth.
Wallet Drainers vs. Traditional Hacks: A Key Difference
It's important to understand that a wallet drainer doesn't "hack" your wallet in the traditional sense of stealing your private key or seed phrase. Instead, it deceives you into giving it permission to take your funds. Think of it like this: a traditional hack is like a burglar picking the lock to your house to steal your valuables. A wallet drainer, on the other hand, is like a con artist who convinces you to sign a document that legally gives them ownership of everything in your house. The attacker never needed your keys; they just needed your signature on the wrong dotted line.
How Wallet Drainers Work: A Step-by-Step Breakdown
To understand how a wallet drainer operates, it helps to use an analogy. Think of interacting with a decentralized application (dApp) as giving a valet the key to your car. You trust them to park it and bring it back. A wallet drainer is a malicious valet who tricks you into not only handing over the key, but also signing a document that transfers the car's title to them. The process is deceptive, fast, and often happens in four distinct steps.
Step 1: The Lure (Social Engineering)
Every wallet drainer attack begins with a hook. Attackers are masters of social engineering, creating tempting situations to get you to click a link. This lure could be a post on X (formerly Twitter) announcing a surprise NFT mint from a famous artist, a direct message on Discord with a link to claim a "guaranteed" airdrop, or a professional-looking ad for a new high-yield crypto protocol. The goal is always the same: create a sense of urgency or excitement to make you act before you think, leading you away from safety and toward their malicious website.
Step 2: The Malicious dApp & Smart Contract
Once you click the link, you land on a website that looks perfectly legitimate. It might be a pixel-perfect copy of a real project's site or a well-designed page for a fake one. Everything from the branding to the text is crafted to build trust. You'll be prompted to do something you've likely done many times: connect your crypto wallet. Behind this slick interface, however, lies a malicious smart contract—a piece of code designed not to provide a service, but to request dangerous permissions over your assets.
Step 3: The Deceptive Signature Request
After connecting your wallet, the dApp will ask you to "sign a transaction" to proceed. This is the critical moment of the attack. Your wallet (like MetaMask or Phantom) will show a pop-up asking for your approval. The text is intentionally confusing or disguised as a normal action, like "claiming tokens" or "verifying your wallet." In reality, you are being asked to approve a powerful permission, often called setApprovalForAll or a similar function. This doesn't send funds immediately; instead, it gives the attacker's contract the authority to move assets on your behalf at any time in the future, without needing your approval again.
Step 4: The Asset Transfer
The moment you click "Approve" or "Sign," the trap is sprung. The attacker's automated script instantly scans your wallet for anything of value—ETH, stablecoins, valuable NFTs, and other tokens. It then executes a series of transactions, rapidly transferring all approved assets out of your wallet and into one they control. This process is automatic and can empty a wallet in seconds. By the time you realize something is wrong, your crypto is gone.
Common Wallet Drainer Scams to Watch For in 2026
Now that you understand the mechanics of how wallet drainers work, let's look at where you're most likely to encounter them. Scammers are master storytellers. They build convincing narratives designed to make you feel excited, rushed, or afraid of missing out. Recognizing these stories is your first line of defense against a wallet drainer crypto attack.
Fake NFT Mints
One of the most popular traps involves the hype around new digital art collections. Scammers create a professional-looking website for a brand-new, "can't-miss" NFT project. They use social media to generate excitement, promising amazing art and huge future value. The site will feature a prominent "Mint Now" button and a countdown timer to create a sense of extreme urgency. This is the classic setup for a fake NFT mint. When you click to mint your NFT and sign the transaction, you aren't creating a new asset; you're approving a malicious contract that gives the attacker permission to empty your funds.
Phishing Airdrops and Token Claims
Another common tactic preys on the desire for "free money." You might see a post on social media or get a direct message about a surprise airdrop from a well-known DeFi protocol or token project. The message directs you to a website that looks identical to the real one. To get your free tokens, the site prompts you to connect your wallet and sign a transaction to "claim" your reward. In reality, that signature authorizes the wallet drainer script to access and transfer your existing assets. The promise of a small gain masks the risk of a total loss.
Compromised dApp Frontends
This method is particularly sneaky because it targets websites you already know and trust. In this scenario, hackers find a vulnerability in a legitimate decentralized application, like an NFT marketplace or a crypto exchange. They don't take the site down; instead, they quietly inject malicious code. You visit the familiar URL, everything looks normal, and you try to perform an action like listing an NFT for sale. The site presents a pop-up asking for your signature, but the code has been altered. If you approve it without carefully reading the permissions, the hidden wallet drainer is activated.
Red Flags: How to Spot a Potential Wallet Drainer
Now that you understand the mechanics of these scams, you can learn how to spot them in the wild. Developing a healthy skepticism is your strongest defense. Think of the following points as a mental checklist to run through before you ever connect your wallet or sign a transaction. This simple pre-flight check can save you from a catastrophic loss.
Unrealistic Promises and Urgency
Scammers often prey on the fear of missing out (FOMO) and greed. Be extremely cautious of projects promising guaranteed, sky-high returns or offering "free" high-value NFTs with no catch. A common tactic is to create false urgency. You might see a countdown timer or a message claiming "only 10 spots left!" This is designed to rush you into making a mistake without thinking. Legitimate projects build communities over time; they don't need to pressure you into acting within minutes. If an offer sounds too good to be true, it is almost certainly a trap set by a wallet drainer crypto scam.
Suspicious URLs and Social Media Accounts
Look closely before you click. Scammers are masters of imitation. Always double-check the website's URL for subtle misspellings, like using "rn" to look like an "m" or adding an extra letter. Bookmark the official sites for projects you use frequently. When you see a project promoted on social media, investigate the account. Does it have a long post history with real engagement? Or was it created last week with thousands of bot followers and generic comments? A weak online presence is a major warning sign.
Vague or Overly Broad Transaction Permissions
This is the final and most critical checkpoint. When a dApp asks you to sign a transaction, your wallet (like MetaMask or Phantom) will show you what permissions you are granting. Read this prompt carefully. If the transaction asks for sweeping permissions, especially one called "Set Approval For All," you should reject it immediately. Granting this is like giving a stranger a signed, blank check to your entire crypto account. A dApp should only ask for permission to access the specific token or NFT needed for the transaction, not your whole collection. This is often the final step in how wallet drainers work, and stopping here is your last line of defense.
How to Protect Your Crypto from Wallet Drainers
Now that you understand the mechanics of these threats, let's move on to the most important part: building your defense. Protecting your assets from a wallet drainer isn't about having complex technical skills; it's about adopting a few key security habits. To protect your crypto, you should:
- Use a hardware wallet to keep your private keys offline.
- Use a separate 'burner' wallet for interacting with new dApps.
- Regularly revoke token approvals for dApps you no longer use.
- Simulate transactions to see their outcome before you sign.
Let's break down each of these practical steps.
Use a Hardware Wallet
Think of your private keys as the master key to your entire crypto vault. A hardware wallet is a small physical device that stores this key completely offline. When you need to approve a transaction, the request is sent to the device, you sign it physically by pressing a button, and only the signature is sent back. The key itself never touches your internet-connected computer. While you can still be tricked into signing a malicious transaction, a hardware wallet prevents the most direct attack: the outright theft of your private keys.
Use a 'Burner' Wallet for Minting
One of the best ways to limit potential damage is to compartmentalize your activity. Create a secondary, non-custodial crypto wallet that you only use for interacting with new or unverified dApps, like for minting a new NFT collection. This "burner" wallet should only ever hold the small amount of crypto needed for the transaction. If that dApp turns out to be a wallet drainer, the thieves can only steal what's in that specific wallet, leaving the funds in your main, high-value wallet untouched. It's the digital equivalent of not carrying your life savings in your pocket.
Revoke Token Approvals Regularly
When you use a decentralized exchange or dApp, you often grant it permission—an "approval"—to spend specific tokens from your wallet. These permissions can remain active indefinitely unless you cancel them. Malicious actors can exploit these old, forgotten approvals. A great security habit is to periodically review and revoke these permissions using trusted tools like Revoke.cash or the token approval checker on Etherscan. This is like changing the locks on your house; it ensures only the people and apps you currently trust have access.
Simulate Transactions Before Signing
A new generation of security tools gives you a superpower: the ability to see the future. Browser extensions like Fire or Pocket Universe simulate a transaction before you commit to it. When you're about to sign, they pop up a clear, human-readable summary showing exactly what will leave your wallet and what you'll get in return. If a transaction looks like it's about to drain your valuable assets for nothing, the simulation will warn you, allowing you to reject it safely. This is your final and most powerful line of defense against a deceptive signature request.
I've Been Hacked: What to Do After a Wallet Drainer Attack
The moment you realize your crypto is disappearing is horrifying. Panic is a natural reaction, but acting quickly and methodically is your best chance to stop the bleeding. If you suspect you've fallen victim to a wallet drainer crypto scam, immediately follow these emergency steps to regain control and prevent further losses.
Step 1: Revoke All Permissions Immediately
First, you must cut off the attacker's access. The wallet drainer works because you granted a malicious smart contract permission to spend your tokens. You need to revoke that permission now. Use a trusted tool like Etherscan's Token Approval Checker or Revoke.cash to see all active permissions and immediately cancel them. Think of this as slamming the door shut and locking it before the thief can take anything else.
Step 2: Transfer Remaining Assets
Once you've revoked permissions, your next move is to abandon the compromised wallet entirely. Create a brand new wallet with a completely new seed phrase. Do not just create a new account within your existing wallet software, as the original seed phrase is likely compromised. Swiftly transfer any and all remaining assets from the old, compromised wallet to your new, secure one. This is the only way to be certain your funds are safe from the original threat.
Step 3: Report the Scam
While recovering your stolen funds is very difficult, reporting the attack helps protect the community. You can report the scammer's wallet address on blockchain explorers like Etherscan, which can flag it as malicious. Also, notify the community where the scam occurred, such as the official Discord or Telegram for the project the scammers were impersonating. While this won't get your crypto back, understanding what happens to your assets and reporting the crime helps prevent others from becoming victims.
Key Takeaways: Staying Safe in Web3
Exploring the world of decentralized applications can be exciting, but it requires a new level of personal responsibility. Protecting your assets comes down to a few core principles of caution and awareness. Keep these key points in mind as you explore, and you'll be much better prepared to identify and avoid a potential wallet drainer.

- Trust, But Always Verify: Before connecting your wallet or signing any transaction, triple-check the website's URL. Scammers are experts at creating convincing fake sites. Always access projects through official links from their verified social media or community channels.
- Read the Fine Print: Every signature request is a contract. Take a moment to understand what permissions you are granting. If a dApp is asking for unlimited access to your funds (like with a
SetApprovalForAllrequest), be extremely cautious. - Use a Burner Wallet: For new projects, airdrops, or any dApp you're not 100% sure about, use a separate "burner" wallet with only the minimum amount of crypto needed for the transaction. This isolates your main funds from risk.
- Practice Good Wallet Hygiene: Don't let old permissions linger. Periodically use a tool like Etherscan's Token Approval Checker to review and revoke active connections you no longer need.
Sources
Author

Crypto analyst and blockchain educator with over 8 years of experience in the digital asset space. Former fintech consultant at a major Wall Street firm turned full-time crypto journalist. Specializes in DeFi, tokenomics, and blockchain technology. His writing breaks down complex cryptocurrency concepts into actionable insights for both beginners and seasoned investors.


